
The cyber defence link you are missing
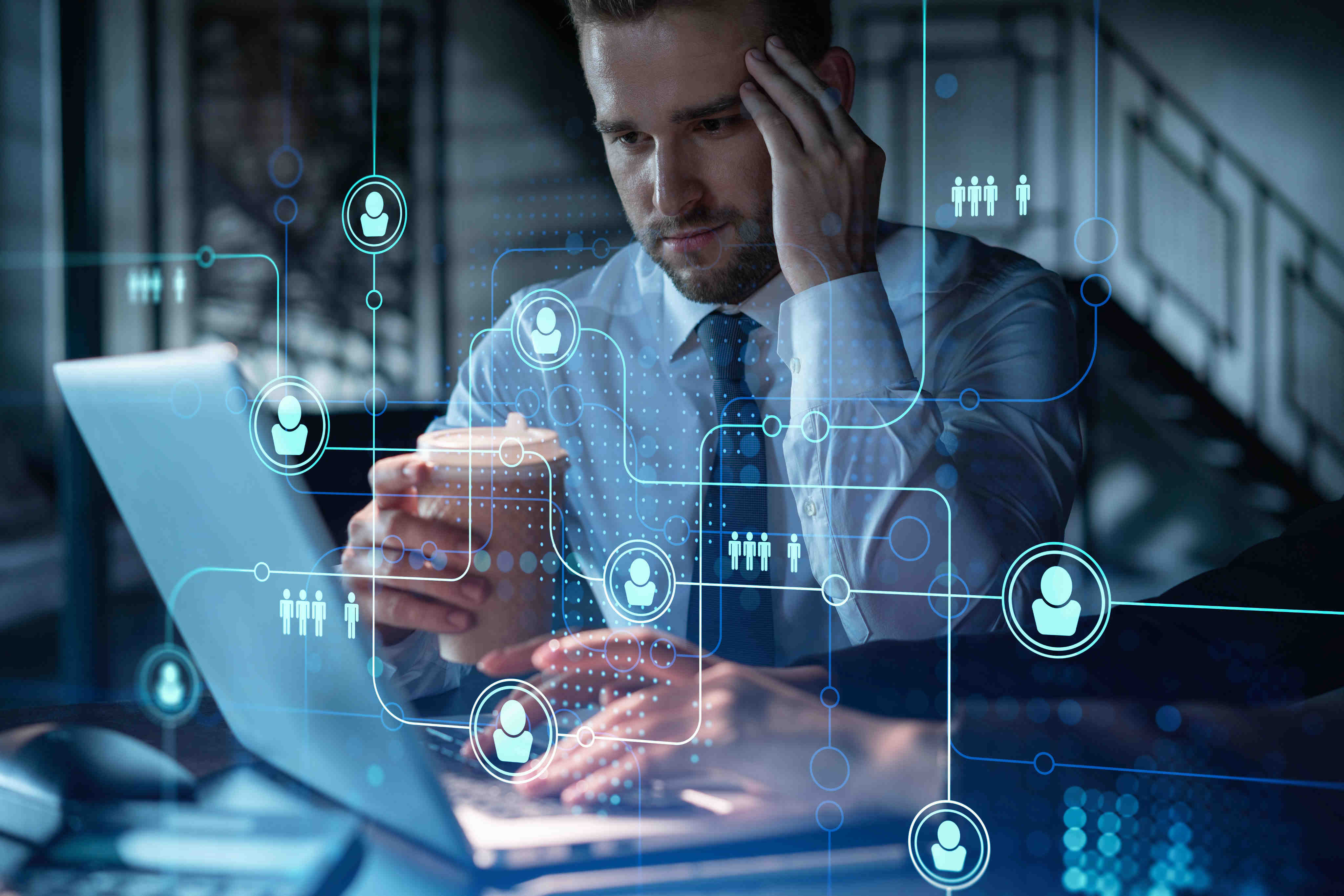
CCS is not a technical cyber range. It is not a tabletop exercise. It occupies the critical gap between them - the layer that no other platform addresses.

Five principles that drive everything we do
Preparedness Beyond Prevention
You've invested in prevention. Now invest in preparedness. Organizations spend heavily on prevention tools. Yet when a breach occurs, the outcome depends entirely on how prepared the people are to respond. CCS addresses the preparedness gap that prevention tools cannot fill.
Experience Before Crisis
Would you rather have a team with experience, or a team facing it for the first time? The number of people who have lived through a real cyber incident is small. The only way to build that experience before the crisis arrives is through realistic, high-pressure exercises.
Realistic Without Risk
Practice real incidents without real consequences. CCS creates a digital twin of your actual environment. Every decision has consequence within the simulation - but nothing touches production systems. Teams can make mistakes, learn from them, and improve.
Organizational, Not Just Technical
Cybersecurity isn't just about tools - it's about people, processes, and decisions under pressure. CCS is the only platform that brings technical teams, incident managers, business process owners, legal, PR, and executive leadership into the same exercise - each experiencing the incident from their own realistic perspective.
Compliance as Capability
Meet regulatory requirements while building genuine readiness. CCS supports NIS2, DORA, and other frameworks - but the goal is not a checkbox. Teams that exercise with CCS are genuinely better prepared to respond when a real incident occurs. Compliance evidence is a byproduct of real capability.
individual
organisational
individual
organisational

How CCS compares
CCS is complementary to technical cyber ranges - not competitive. It addresses a different layer of the problem: organizational coordination and decision-making, not individual technical skills.
| Tabletop | Cyber Range | CCS | |
|---|---|---|---|
| Scenario realism | Hypothetical discussion | Live system interaction | Dynamic, time-pressured simulation |
| Technical infrastructure | Not modelled | Full system emulation | IT/OT digital twin |
| Business impact | Estimated, not modelled | Technical metrics only | Modelled with financial metrics |
| Executive participation | Possible | Not suited | Designed for it |
| Objective outcome data | No recorded data | Technical performance metrics | Full structured data log |
| DORA/NIS2 evidence | Weak audit trail | Limited compliance focus | Structured documentation |
| Reusability | Full re-preparation each time | Significant setup per exercise | Landscape reused indefinitely |
| Time required | Half day | Days to weeks | 3–6 hours |

Exercises are no longer optional -
they're required
CCS directly supports compliance with mandatory cybersecurity frameworks that require organizations to test and demonstrate their incident response capabilities.
EU NIS2 Directive
Requires organizations in critical sectors to implement cyber exercises as part of their security measures and incident handling capabilities - across 18 sectors.
DORA
Mandates financial entities to conduct regular operational resilience testing, including scenarios for ICT-related incidents and their business continuity impact. Mandatory since January 2025.
ISO 27001
CCS exercises generate structured exercise data - event logs, decision records, and communication history - providing the documented basis needed to satisfy regulators and auditors.
NIST CSF
Scenarios can be designed to simulate the specific threat scenarios most relevant to your regulatory obligations and sector-specific risk profile.

See how CCS fits your
specific regulatory requirements.